If Cwtch had Arti
Searching for the Best Union of Tor and Encrypted Messengers
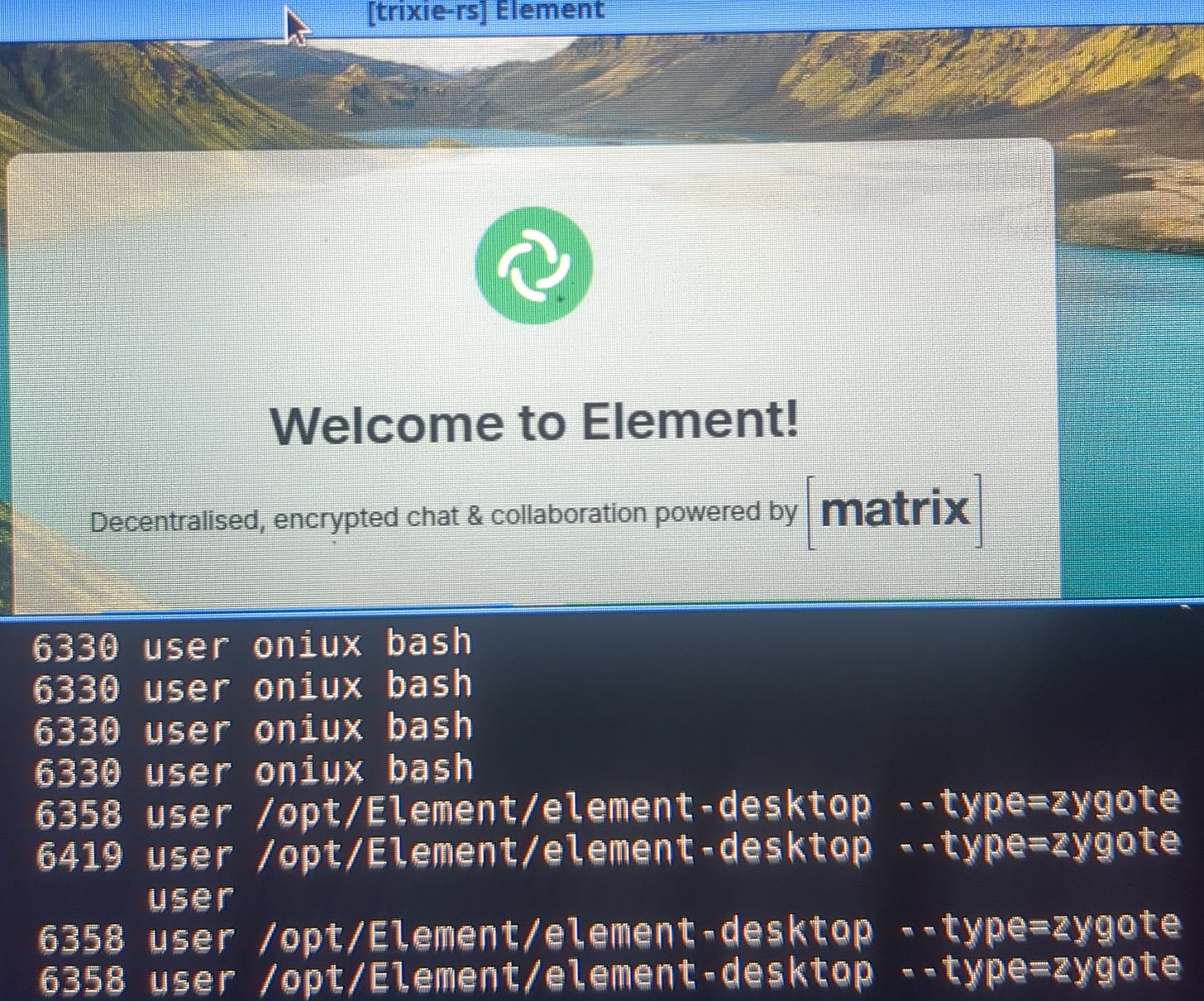
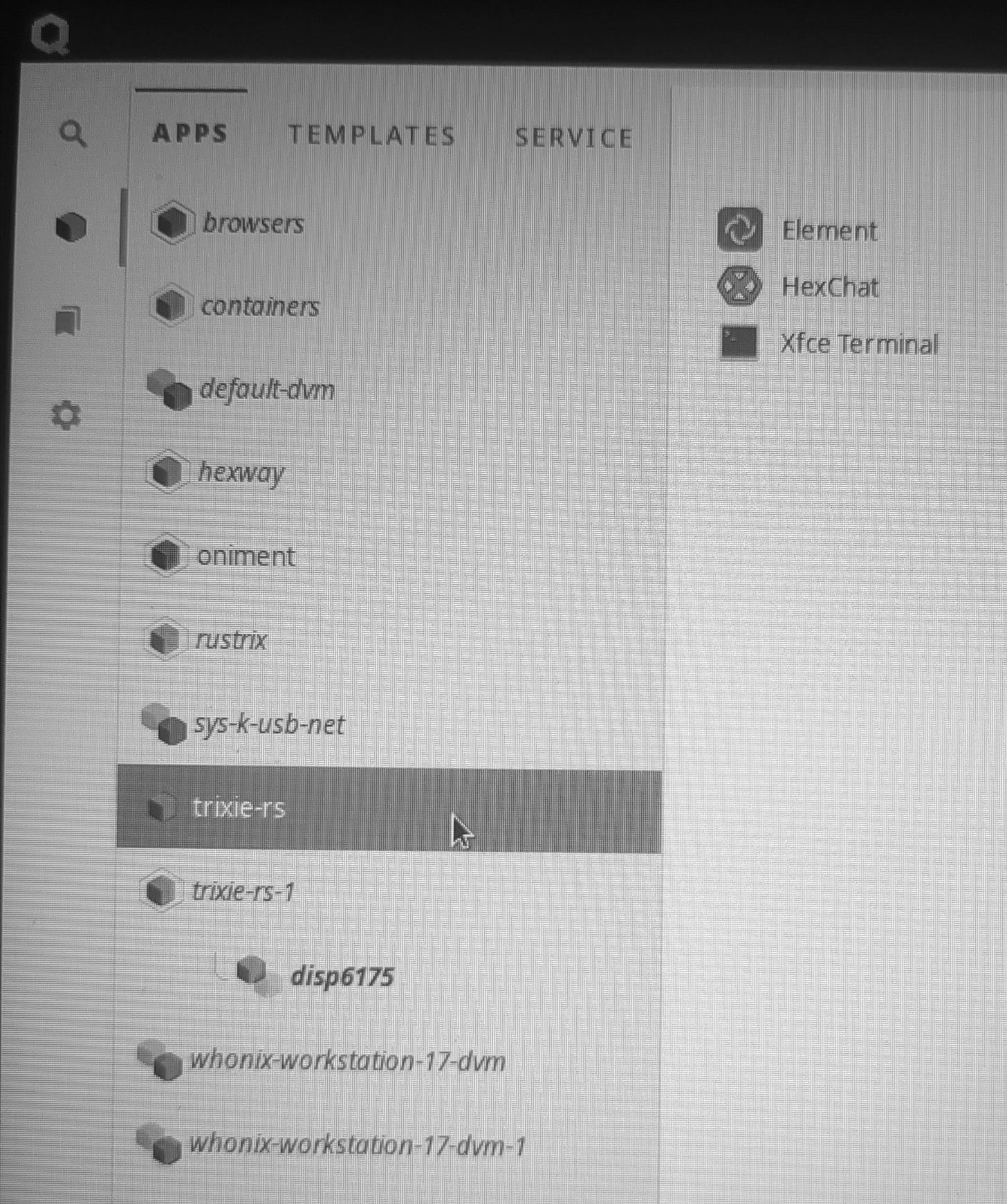
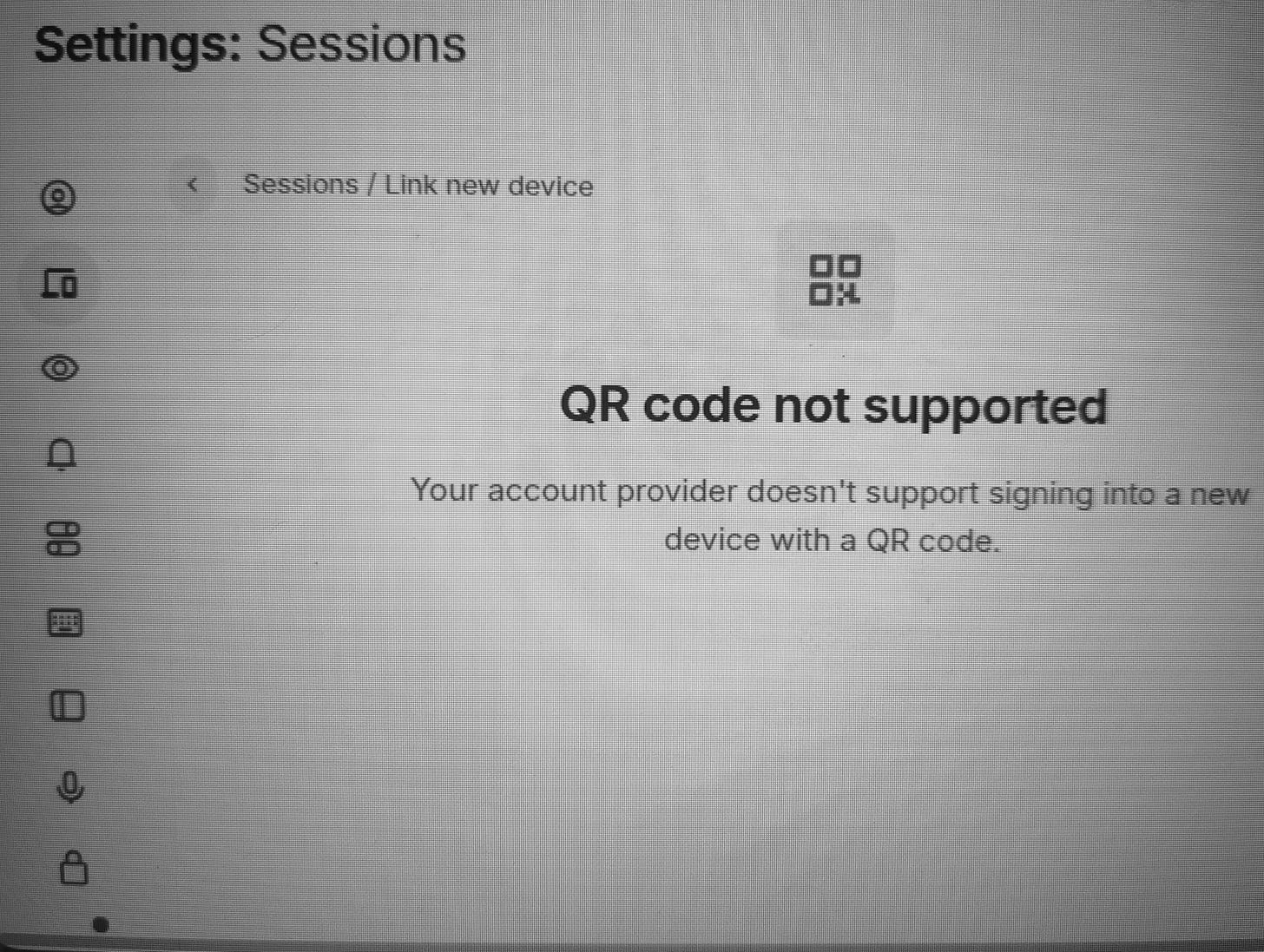
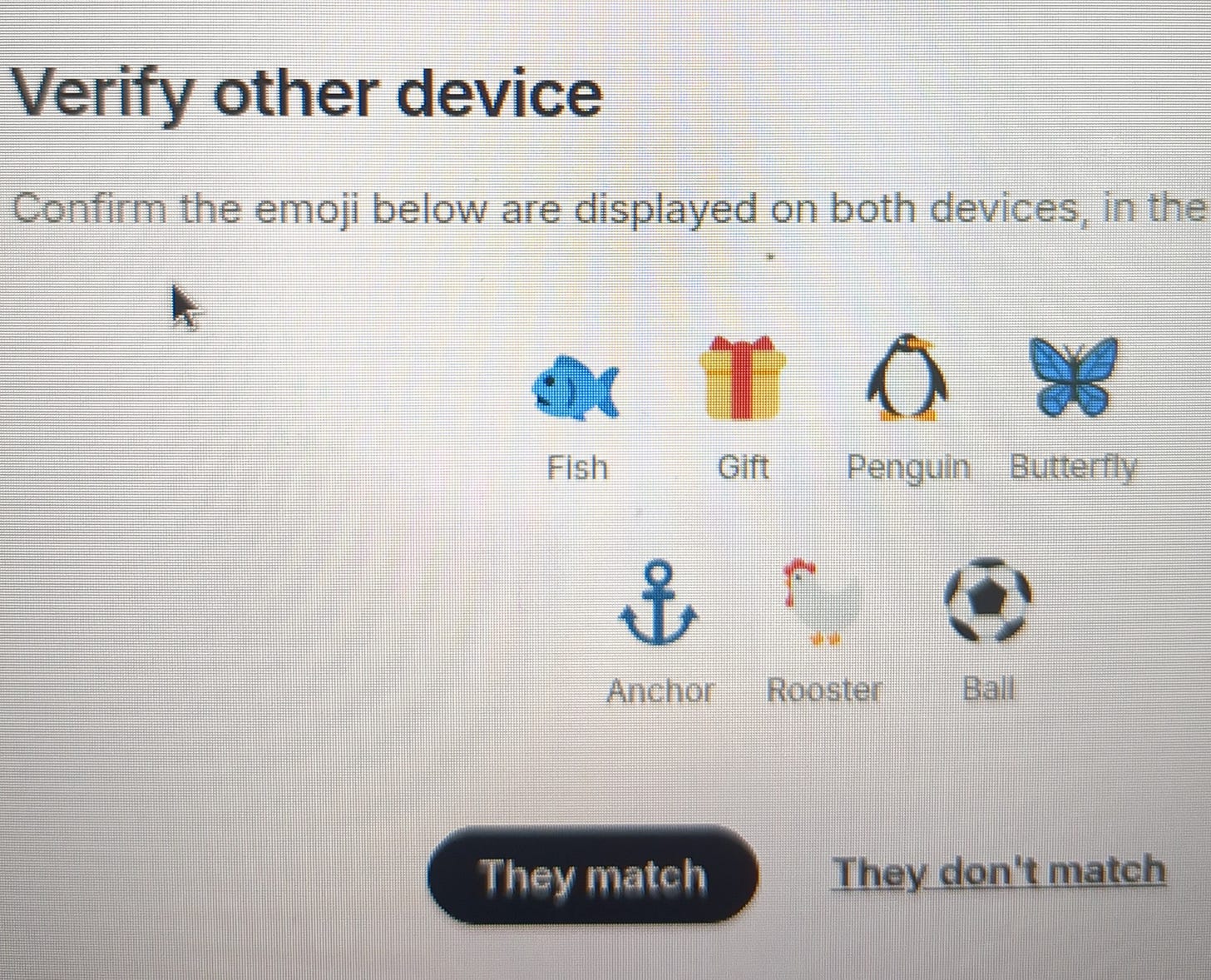
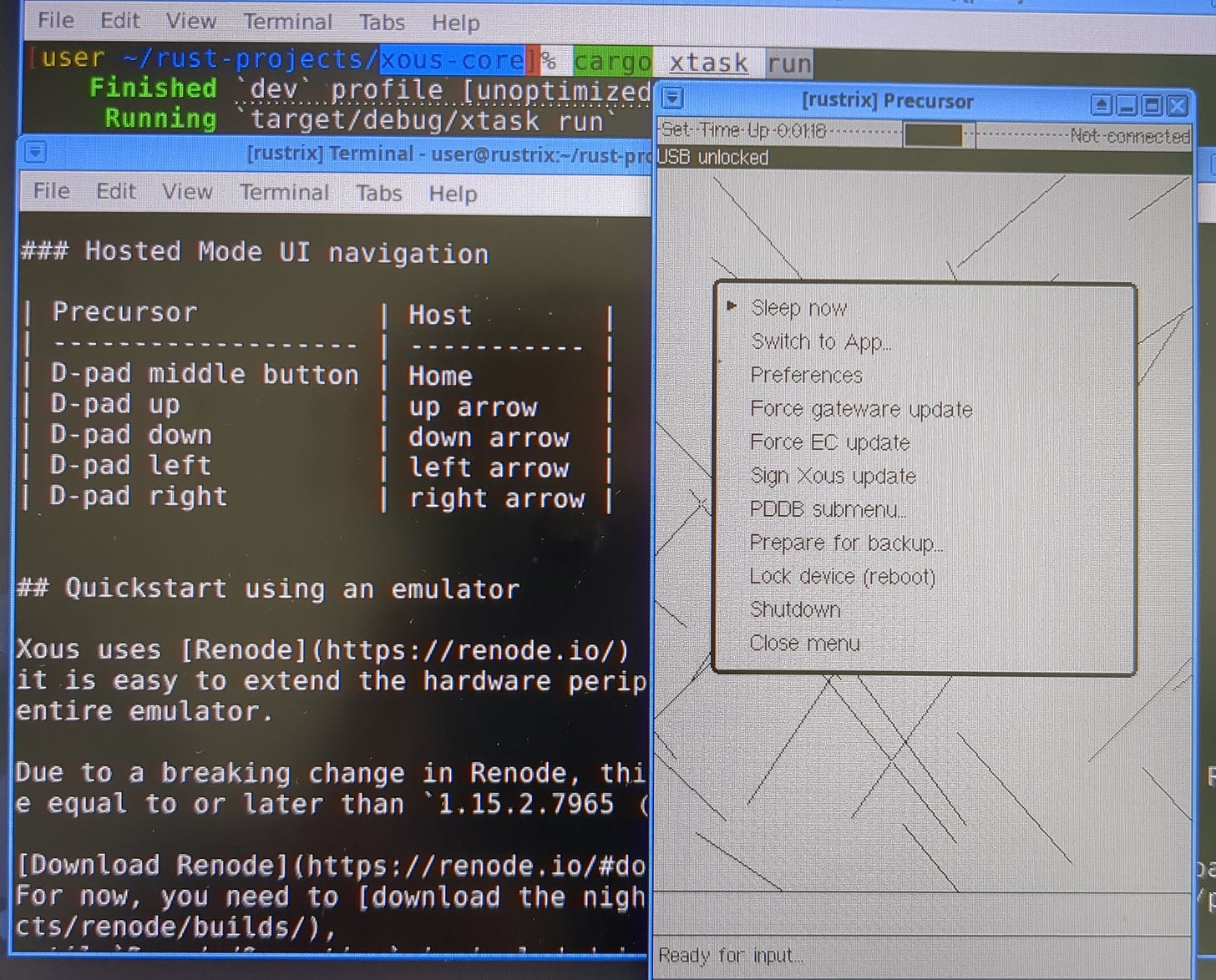
Oniment Trixie: Element Messenger through Oniux after Huang's Mtxchat in Xous
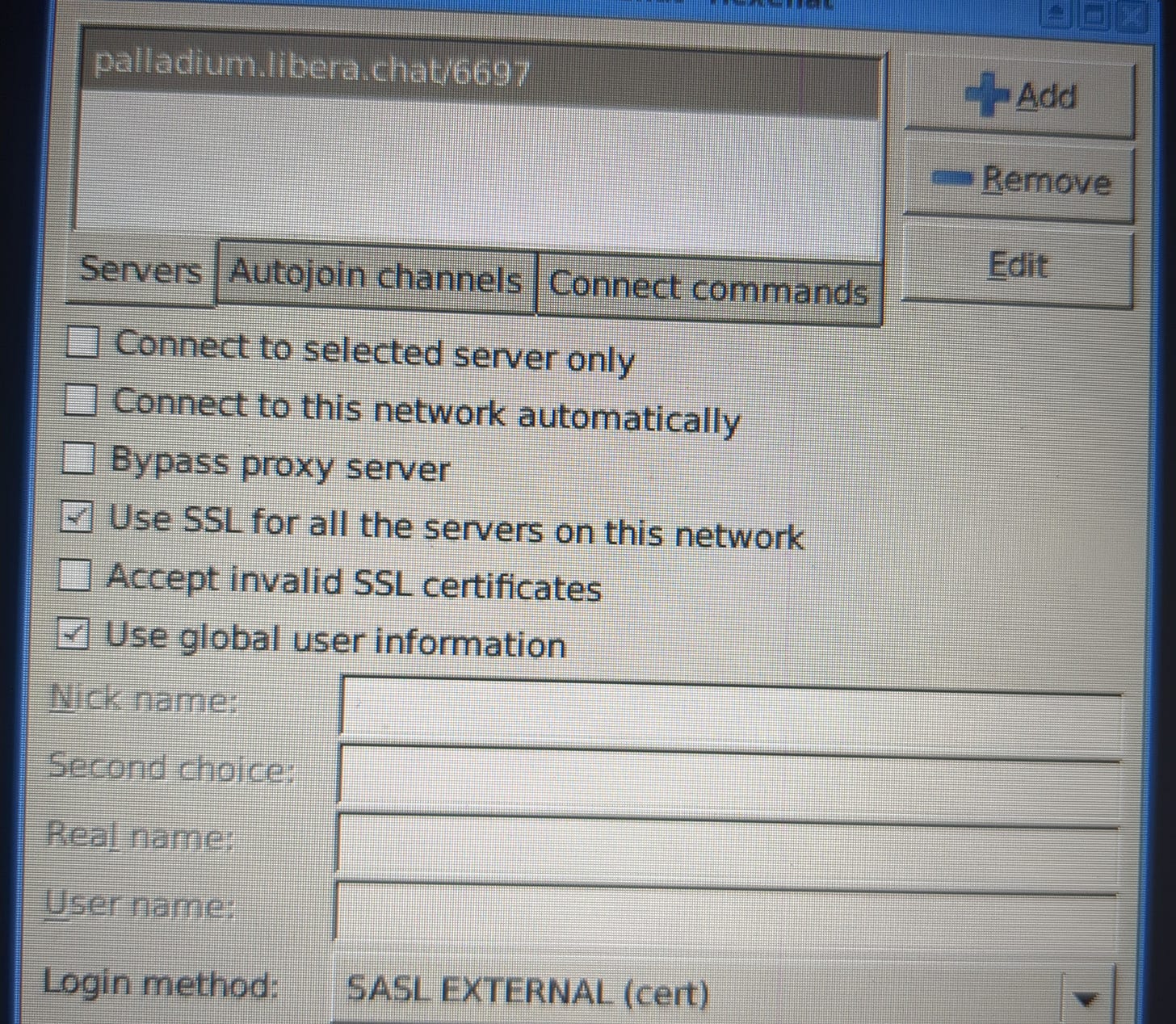
Truly anonymous messaging is very difficult, particularly if you have been designated as a person of interest and are already under intensive surveillance. The Matrix servers and protocol (Element app/client) require email verification to participate just like IRC (Hexchat). Both protocols will require some form of initial identification before the servers will alow you to use Tor with the clients. You could use a temporary email address to sign up, but that could be traced back to your permanent email which is linked to your phone by SMS or even to digital behavior fingerprinting (keystroke, diction, etc).
In the case of IRC, the irssi program is first used to register your email and password with NickServ before you can use the IRC channels and this process has to happen without Tor. There are DNS proxies and VPNs to mask some information, but that does not present much of an obstacle to Nation State cyber threats.
Even if SMS is out-of-band and different from the networking path of the service you are trying to register with, like email verification, SMS and email codes are not encrypted end to end and a race condition could be met in which the large-scale cyber threat can get to your pass codes before you do. Additionally, the server owners might revoke your password against your wishes. They will claim that it is their server and you are just a user. Their perspective becomes—and I think deep and dark forces put them up to it—
since I can re-write history, you forgot.
Ladies and gentlemen, they have the devs. They have the servs. Revoking history puts the robbed to shame. For the time at least.
So once you get your authentication squared away, and then reconfigure it to meet Tor’s requirements, it is possible to use Socks5 localhost:9050 just like in Telegram after you have verified and linked to your phone with SMS. Using Tor in all these forms of chat is using an anonymity network in combination with an identifier. Does that really make sense? TLS is strong encryption also, but Tor is now Quantum Safe with the ed25519 curve. The situation is similar to alpha Tor, using security keys with Tor Browser, specifically identifying yourself on an onionsite. People do do it.
But none of that is about Oniux specifically, the next generation of Tor written in Rust. When the Tor Project blog says to just try and # oniux hexchat, it is not that simple. How do you think you are going to edit the torrc for the palladium LiberaChat onionsite when the Rust has already been compiled? TLS over Tor after you have already authenticated without Tor is probably about as good as it is going to get for most people who would even bother trying to create secure lines of communication. Also, consider that the Libera Chat network with its rotating element-named subdomains is already an anonymity network. It might actually be pretty hard to dramatically best TLS in such a network. Time to juxtapose network analytics for a conclusive judgment.
Protecting Phones Against Malware and Spyware
An excellent talk about phone security with Tor project leaders can be found here.
.onion address for The Tor Project —> http://2gzyxa5ihm7nsggfxnu52rck2vv4rvmdlkiu3zzui5du4xyclen53wid.onion/privchat/chapter-5/
When governments start posturing as though they will arrest bloggers and crack down with libel laws, isn’t it time to secure your conversations?
(min 23:00) - This is where lawmakers come in to regulate mercenary malware, in a positive inversion reminiscent of the crypto arms embargo that is proposed every time the fascists can’t violate our rights so easily. (30:00 ; 1:04:00)
Dingledine - every time there is a conflict they call it “terror”

There are no push notifications in Cwtch, so you have to coordinate a shared time with your contact. Agree upon a time to talk at various intervals when you will both be online or use another messenger to ping your contact and then move the conversation to Cwtch.
With Cwtch, you just need to have the local Cwtch client and know the onion address of your contact. The onion is the ver. There is no need for further verification other than the chain of binding trust in the Tor network, assuming that the right person got your onion address. A client establishes a binding connection to Tor and Tor connects to the onion address.
Cwtch is written in Go. Ideally, it would be written in Rust. But ask yourself, what does the “API” of an adversary look like if they are taking advantage of programming language properties like memory safety? It is not like they are an ISP injecting into an SSL strip downgrade. Endpoint attackers with tailored targets? Certainly advanced Nation State actors.